
Implementation of Firewall Policies FortiGate (Part 2) Hacking Articles
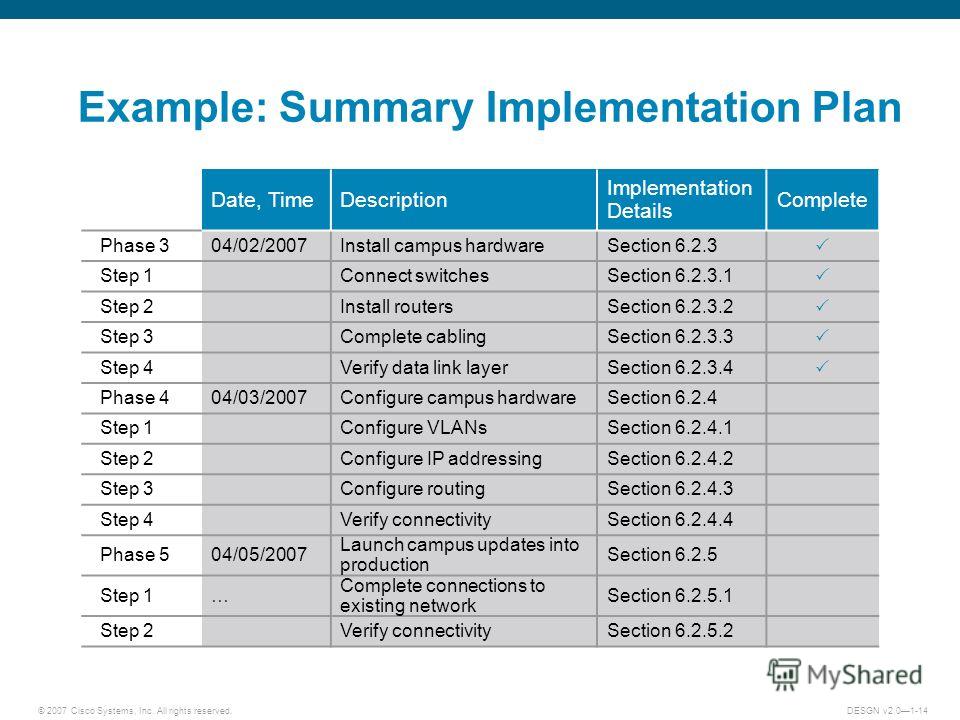
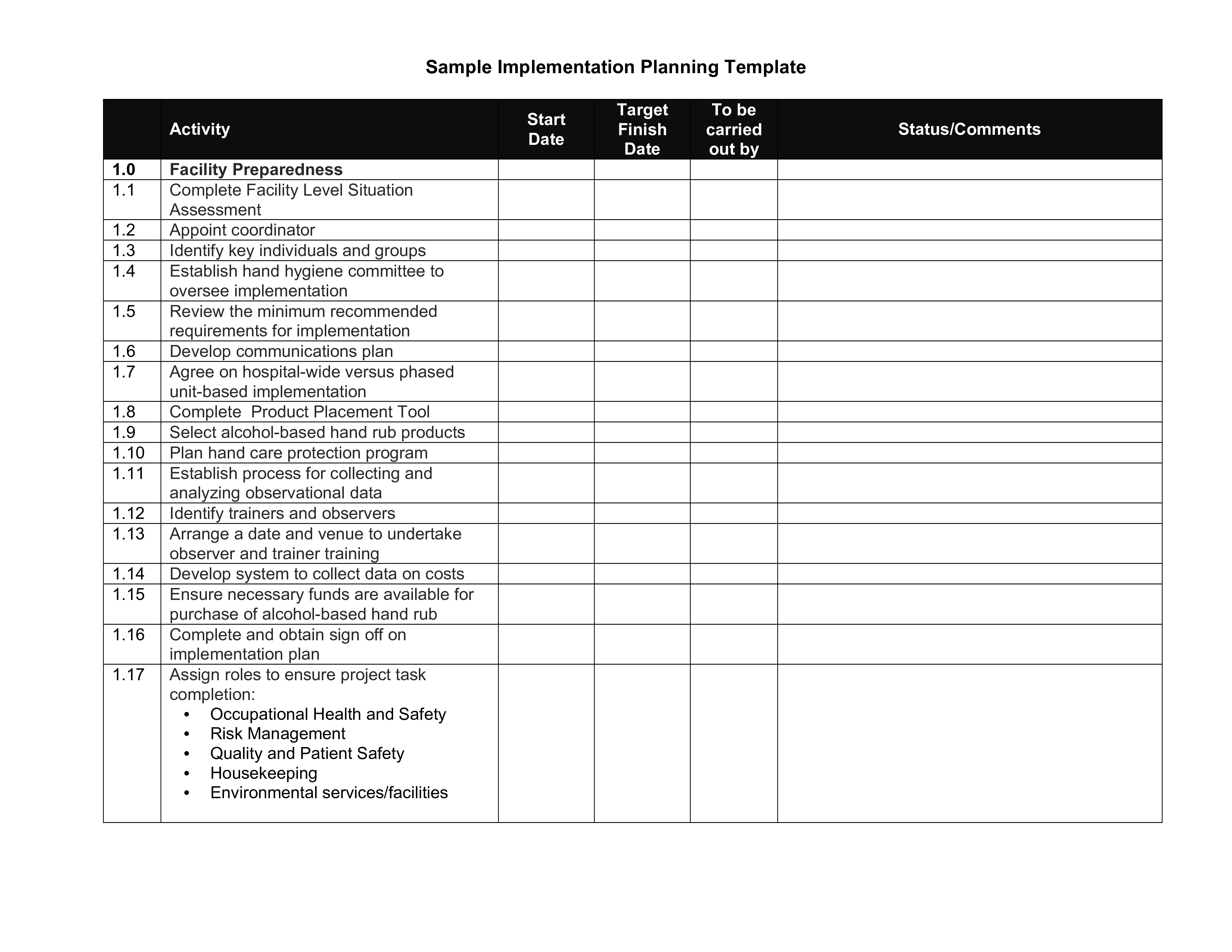
Planning and design come together in mapping business solutions that actually address objective needs. These phases look at different angles to see if actual issues have been addressed, taking into account cost, timing, and ROI evaluation. Design and implementation include final review of design and timelines, beginning stages of project
It Network Implementation Plan Template Peatix
Design the firewall system. 7 2. Acquire firewall hardware and software. 23 3. Acquire firewall documentation, training, 27. Implementation details How an organization adopts and implements the practices often depends on. ERP (enterprise resource planning), just-in-time inventory controls, and electronic mail
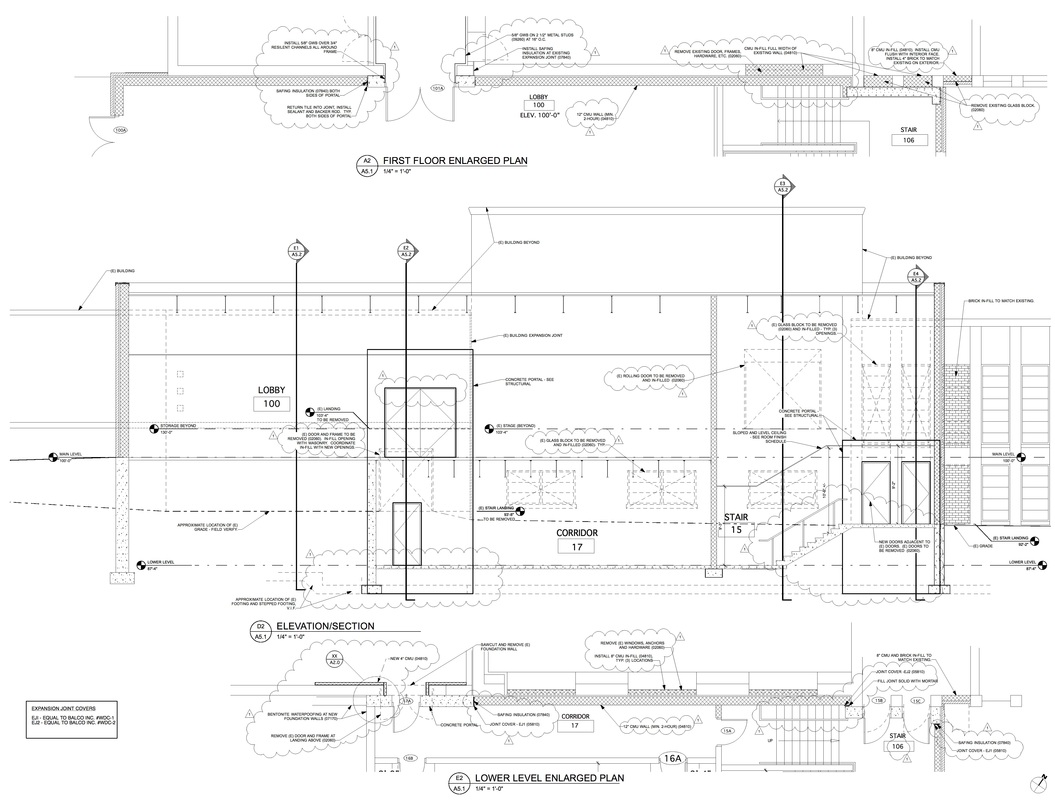
Wiki Blog Architekwiki
3. Installation, Configuration, and Maintenance of the Firewalls. Once a vendor has been chosen, the final step in setting up your firewall is the actual implementation. The IT provider you have chosen will install the solution in your environment, covering all of the areas you deemed necessary in your earlier assessment.
Hardware Firewall Explained englshrini
implementation of your Palo Alto Networks firewall to maximize its effectiveness. Our certified team of experts will help you navigate the daunting task of firewall policy and configuration, and support the smooth migration of your existing firewall configurations. Our real-world experience designing, implementing, and operating
Network Firewall Implementation & Configuration Service CARE IT
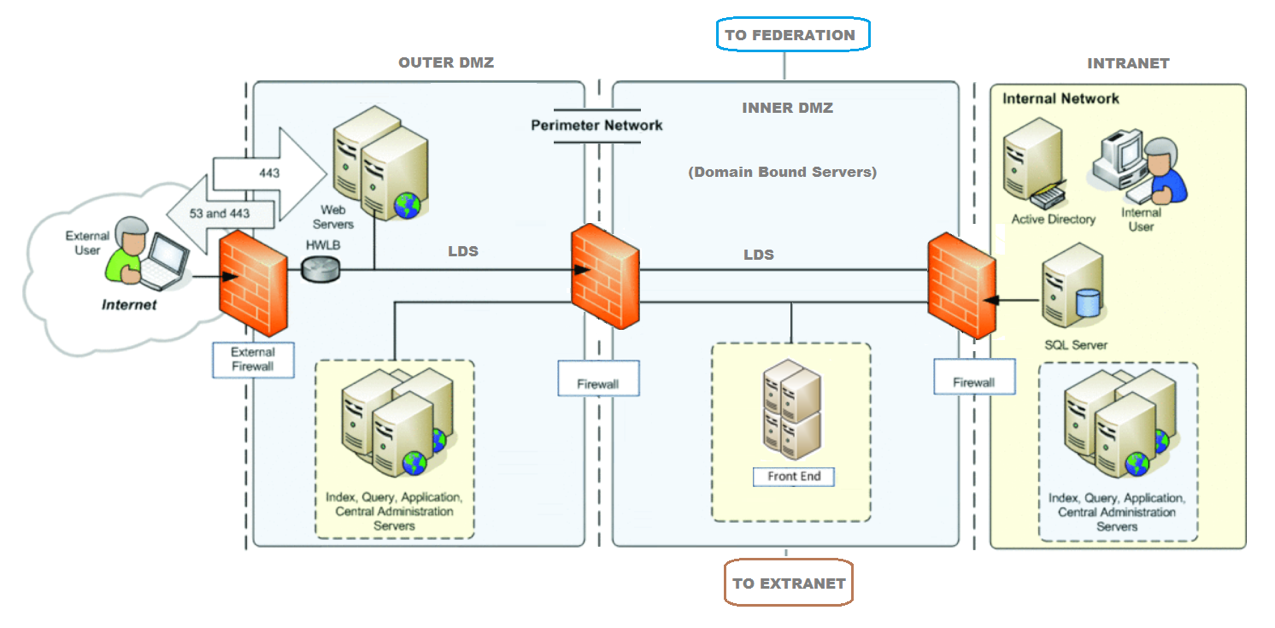
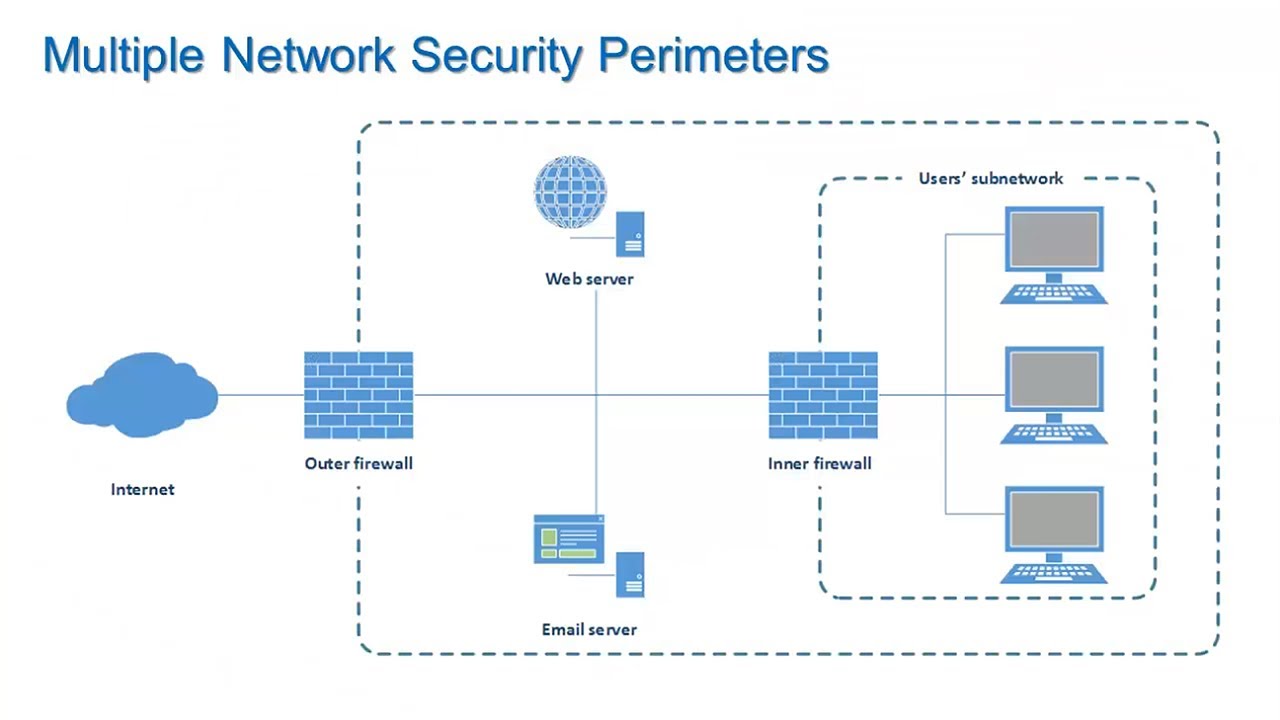
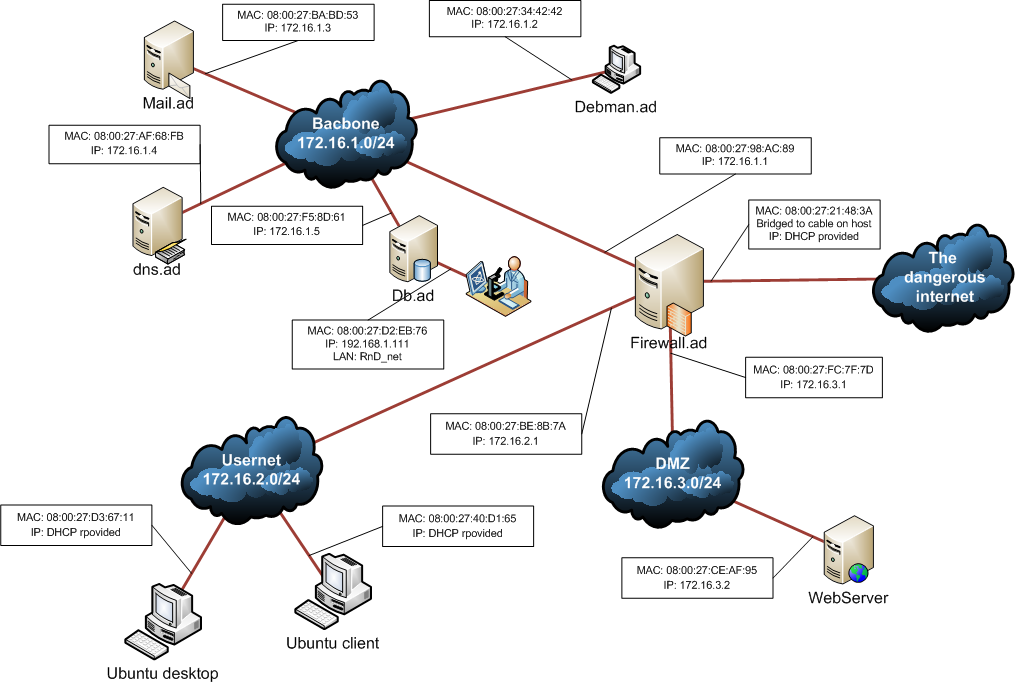
Firewall is a system designed to prevent unauthorized access to or from a private network. They can be implemented in both hardware and software, or a combination of both.. In our implementation, we have used the struct ip structure as an header to the payload that is sent. ip is a struct (structure) in the C programming language..
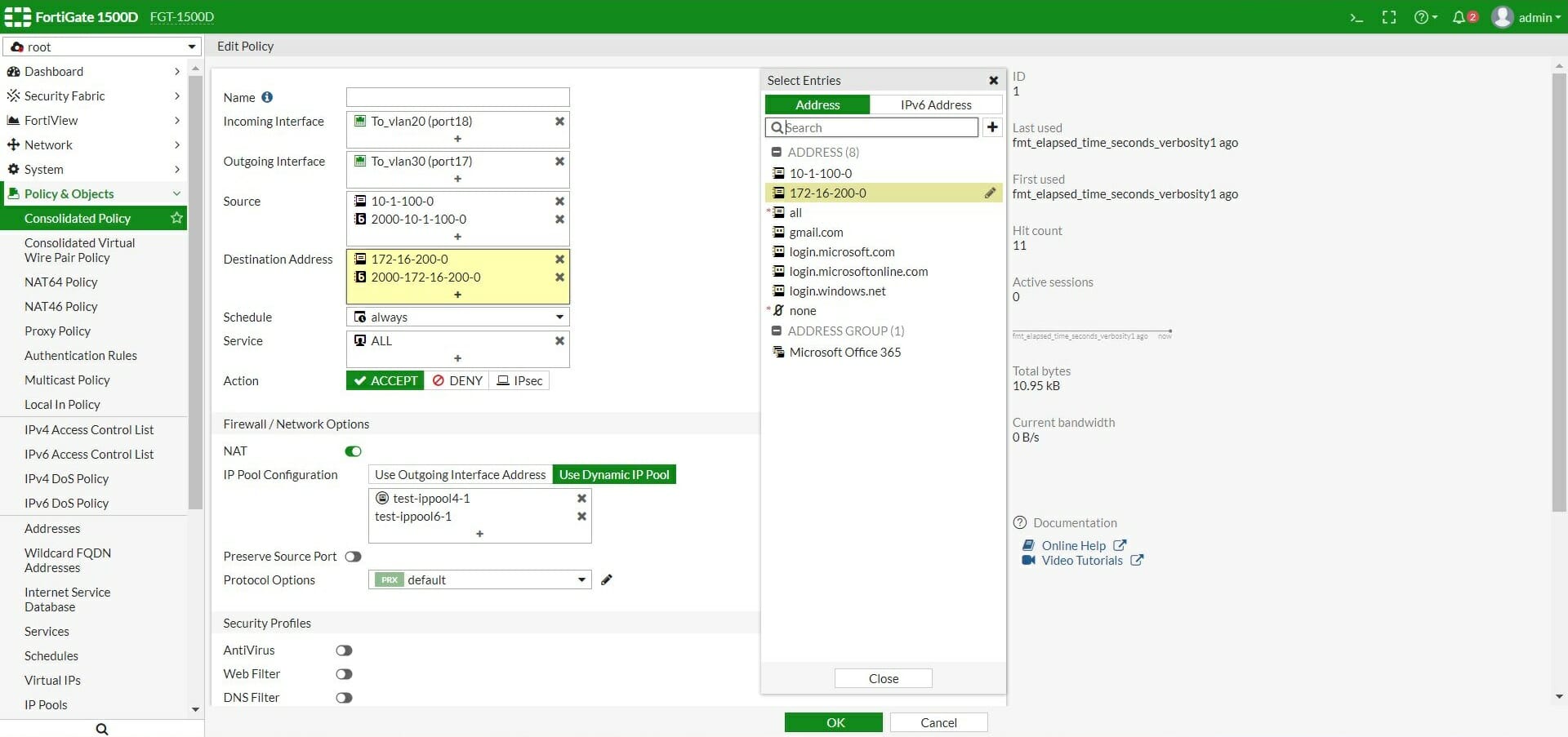
Implementation of Firewall Policies FortiGate (Part 1)
Our project approach. Below you can see an example of a 7-step approach to a firewall migration plan. The plan applies, whether it is an external firewall providing perimeter security or an internal firewall solution defending your internal network segments. 1 - Understand. The first step in a project such as this is to understand your business.
Firewall Migration & Replacement Project Manx Technology Group
Outcomes of the firewall implementation planning phase will determine how to best configure and deploy firewalls into production. Firewall Configuration. The next phase of firewall design and implementation is configuring firewalls and integrating them into your organization's security architecture. The NIST recommends several processes for.

How to Replace Your Firewall (Firewall Migration Plan) (2022)
Here's how ClickUp's Firewall Implementation Project Plan Template can help your IT department: Streamline the entire implementation process, from initial setup to final testing. Assign tasks and deadlines to team members for efficient collaboration. Monitor progress and track milestones to keep the project on schedule.

Firewall Management Essentials Change Management 推酷
Firewall Implementation & Maintenance Practices Best Practice Checklist Understanding the basics: A layperson's guide and checklist for overseeing IT. An exclusive publication of Sandbox Technologies, Inc. 4111 West Alameda Avenue, Suite 605 Burbank, CA 91505 Tel. (424) 207-5130 www.sandboxtech.com

Project Deployment Plan PowerPoint Template PPT Templates
Configure a best-practice security policy rulebase to safely enable applications and protect your network from attack. Go to the Best Practices page and select security policy best practice for your firewall deployment. Set up High Availability —High availability (HA) is a configuration in which two firewalls are placed in a group and their.
Firewalls and Network Security Information Security Lesson 7 of 12
The Country-wide Established of Standards and Technology (NIST) recommends a five-stage approach that enterprises can apply for robust firewall design and implementation: Planning firewall design and implementation to meet securing needs; Configuring firewalls in shift with an firewall policy; Testing firewalls up optimize layouts
Sample Implementation Plan Gratis
Figure 1: Five best-practice steps to optimal firewall design. Step 1. Identify Security Requirements for Your Organization. Before you can secure your network environment, you need to understand your organization's resources and security requirements, and your current security posture.
Final Demo Plan Firewall Project
There are many considerations that organizations should include in their firewall selection and planning processes. Organizations need to determine which network areas need to be protected, and which types of firewall technologies will be most effective for the types of traffic that require protection. Several

Project Implementation, Control, and Closure StudiousGuy
For this project, your group will play the role of a consulting company hired to design and test firewalls for corporate networks. The project will have two phases. In Phase I, you will be presented with a network and a set of requirements and asked to produce a firewall that protects the network whil e meeting the functional requirements.

Firewall Adalah Pengertian, Fungsi, Jenis, Cara Kerja dan
WaTech plans to manage the NextGen Firewall Implementation project in two phases. During Phase 1, from Feb. 2023 to Sept. 2024, WaTech will: Refresh core and edge firewall hardware and migrate all existing production traffic to the new hardware. Consolidate equipment and migrate existing edge Intrusion Prevention (IPS) functionality to the new.

Firewall Implementation Neelatech
3. Pick the Vendor and Hardware - Enterprise-Level vs. Mainstream. There are many firewall vendors and products in the marketplace, each with their own strengths and weaknesses. Examine your sizing, business requirements, network complexity, and other factors to determine which firewall is right for your organization.